Strategy for Implementing an Earned Value Management System (EVMS) on a New Project
H&A is often called in to help our clients resolve a myriad of issues with the design or implementation of their EVMS on a project. This is typically during the project’s execution phase when they belatedly realize the project work organization and planning approach was not adequately defined. Project personnel often lack sufficient direction during the project definition and start-up phase. The root cause was the lack of an integrated program/project plan produced immediately following contract award that would have provided the necessary guidance to the project team on how to implement the EVMS using the project control tools of choice to fit the unique requirements of the project.
The advantage of working with a wide range of clients for over four decades is that H&A has the benefit of observing strategies that companies with a commitment to excellence in project management have implemented. The goal of these companies is to ensure project teams have the necessary guidance they need immediately following contract award or authorization to proceed.
Common Components
One of the best strategies H&A earned value consultants have observed at client sites included establishing a core support team whose charter was to ensure the efficient implementation of standard integrated project management practices and tools on all projects. This began with the decision to bid on a contract and flowed through the processes of producing the proposal, initiating the start up activities immediately following contract award, transitioning to the execution phase, supporting the execution phase business rhythm, and conducting self-surveillance. This core team eliminated the functional, process, resource, and data silos that typically exist between new business development, bid and proposal, and project execution. They provided the single focus on the underlying project management approach to ensure project success and a happy customer as well as to meet target profit goals. They also ensured the EVMS was actively maintained to reflect advances in processes, managing data, and software tools.
There are a few common attributes to this approach. For example, these companies:
- Have a proven and established standard, repeatable processes in place. Project personnel are continuously trained on these processes and standard practices using a standard set of schedule, cost, analysis, and risk tools. This may also include standard Agile tools.
- Have established a cross-functional core team whose roles and responsibilities are focused on providing targeted support to proposal and project teams when needed. The composition of the core team reflected the products or services unique to the client. The core team members included subject matter experts (SMEs) from systems engineering, technical disciplines, risk management, finance, contracts, scheduling, cost estimating, EVMS, material management, manufacturing, and Agile. They provide the consistency in approach for the entire project life cycle as well as across projects.
- Have templates and other assets available for project teams. This saves time and helps to establish a common framework for organizing and planning project work effort. This included schedule and cost software tool configuration templates to ensure new projects are set up properly in the tools for integrating data and producing data deliverables. Common utilities or automated interfaces were in place to extract data from business systems such as accounting or the M/ERP system for use in the EVMS.
- Established a “hand-off” process between the proposal team and the project team after contract award with the objective of establishing the performance measurement baseline (PMB) as quickly as possible. The project team could start with the source data and other content from the proposal submission and modify the source content as needed to reflect the negotiated contract. This typically included the WBS, technical and management approach, functional organization requirements (staffing plan), integrated master plan (IMP), integrated master schedule (IMS), cost basis of estimates, risks and assumptions, as well as subcontractor and material requirements. This significantly reduces the time required to produce the PMB and increases the quality of the schedule and cost data.
- Conducted internal and external kick-off meetings with the government customer to ensure everyone on the project team had a clear understanding of the scope of work, deliverables/components, major milestones, major assumptions, required resources, roles and responsibilities of the organizations involved, identified risks, timing and sequence of activities, time frame to complete the work effort, and target budget. Many contracts include the requirement for a post-award conference for just this exact purpose.
Time and Cost Benefits
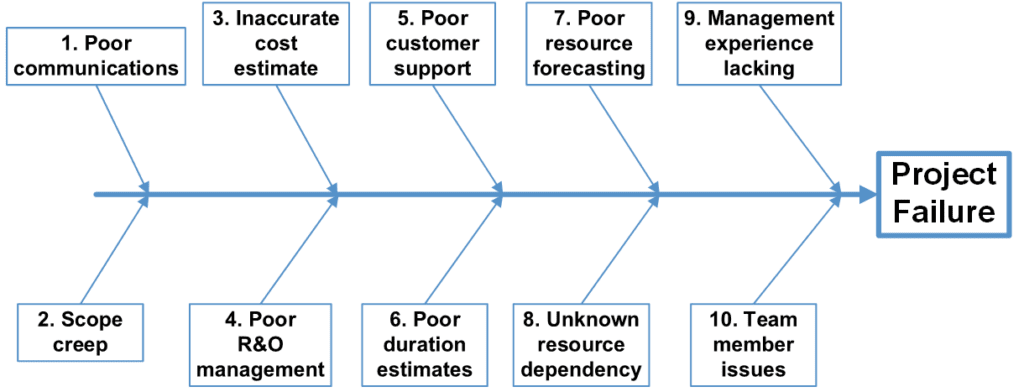
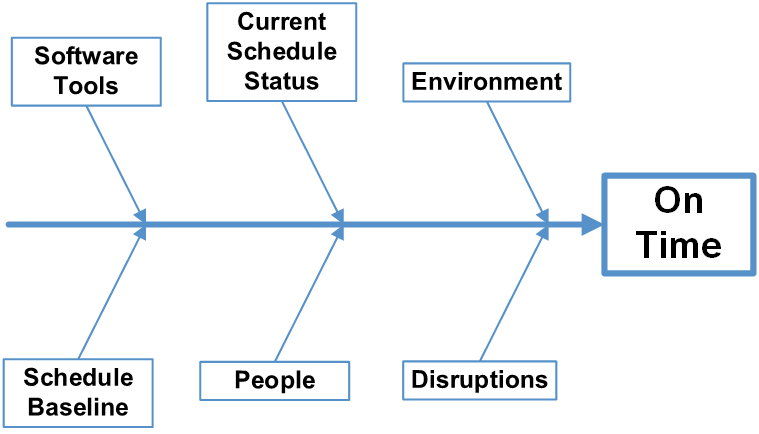
The time and cost benefits of this approach aligns with H&A observations. The following images illustrate the results from informal surveys H&A earned value consultants have routinely conducted over the years. A “big bang” or accelerated approach to implementing an EVMS is better way to go – get it done and move on. The objective is to get the PMB in place as soon as possible and quickly settle into the execution phase. It may take more personnel up front; however, the time frame is shortened. Figure 1 illustrates where there is a short burst of dedicated personnel for three months to get the project team off and running. The support team then moves on to the next project.
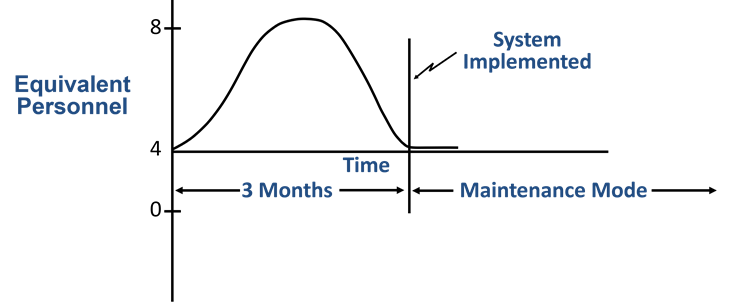
Figure 1: Accelerated EVMS Implementation
As Figure 2 illustrates, it often takes twice as long with a slow ramp-up. In this example, six people are supporting the project for the foreseeable future instead of enabling the project team to function on their own. The project team is continually in a catch-up mode because they haven’t committed to a standard process. It takes longer to get the PMB in place. Data quality is often compromised when the team lacks clear direction on how to proceed or is struggling with how to use the software tools. The support team must remain in place for an extended duration to provide direction to the team on a multitude of levels which limits their ability to help other project teams.
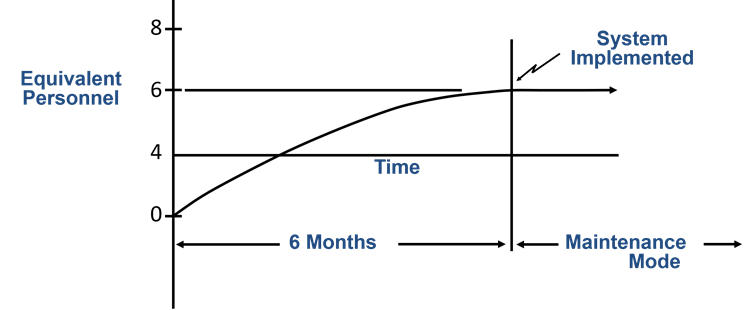
Figure 2: Incremental EVMS Implementation
Things to Consider
Granted it takes time and resources to establish a core team, define all the components, and execute this approach at the corporate level. This is dependent upon management’s commitment to a given level of program/project control excellence and their desire to ensure they have reliable and useful data on all projects for management visibility and control regardless of EVM reporting or EVMS contractual requirements. Usually an internal return on investment (ROI) analysis provided the fact-based information needed to determine it was more cost effective to establish common repeatable processes and standard tools with a cross-discipline core support team. It was a much better alternative than ad-hoc project control implementations or unrealistic schedule/cost baselines that resulted in ugly surprises in the forecasted completion date and estimated cost at completion or contractual penalties that ate into the company’s profit margins.
How do you get started?
You may or may not be in a position to establish a cross-functional project management core support team. An option is to incorporate some of the elements these core support teams use to improve your company’s project management practices. Target areas that can help the project teams to be more efficient or to implement repeatable processes and eliminate ad-hoc approaches where possible. Examples include:
- Establishing a set of templates for new projects that reflect the requirements identified in your EVM System Description. This could include common artifacts such as a WBS Dictionary, forms such as a work authorization document or baseline change request, or outputs such as a variance analysis report. Include these templates and examples on how to use them in your scheduling and EVM training courses.
- Establishing a standard new project configuration template in the schedule and cost software tools of choice that provides a common coding structure foundation with options to incorporate project specific requirements. There could be one or more templates depending upon the work scope or type of contract. The objective is to ensure the tools are properly configured to enable schedule and cost integration and there is a standard base framework for organizing and coding the data. An established base framework also makes it easier to perform cross-project or portfolio analysis using business intelligence tools and generative AI tools.
- Conducting a project kick-off meeting with the customer immediately following contract award to ensure the project team has a common understanding of the contact scope of work, requirements, and objectives. This helps to establish open communications with the customer from the beginning to clarify assumptions and expectations, confirm roles and responsibilities, and identify likely risks as well as risk mitigation strategies.
H&A earned value consultants routinely assist clients to define successful strategies and tactics for designing and implementing a best in class EVMS in a variety of business environments regardless of the client’s point of departure. One of the best opportunities for establishing a best in class EVMS occurs with clients who are new to EVM and are beginning to sort out what they need to do. Other clients often need to do a refresh of their EVMS and how they train their project personnel to improve the effectiveness of their system. As noted in a recent blog “Earned Value Management (EVM): How Much is Enough? ”, maintaining the status quo is a myth – an EVMS requires constant improvement in areas critical to success.
We can help you determine the right strategy for your situation. Call us today at (714) 685-1730 to get started.
Strategy for Implementing an Earned Value Management System (EVMS) on a New Project Read Post »